One of the new features of the upcoming 0.8.6 version of the Profiler is the validation of resources. This means the Profiler verifies the integrity of resources and lets the user inspect problems, making it easy to discover things like appended files or fake resources. This feature comes handy since very often malware is hidden in resources and droppers often use resources to store their payload.
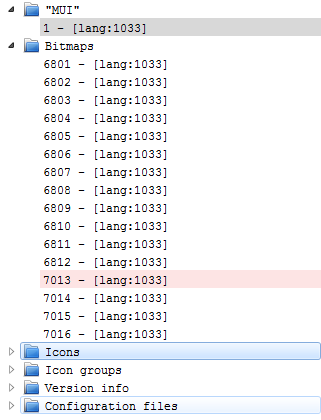
All the most important resource types are supported:
- Version info
- Bitmaps
- Icons
- Cursors
- Icon groups
- Cursor groups
- Configuration files
- Accelerators
- Menus
- Dialogs
- String tables
- Message tables
- Any other supported file format
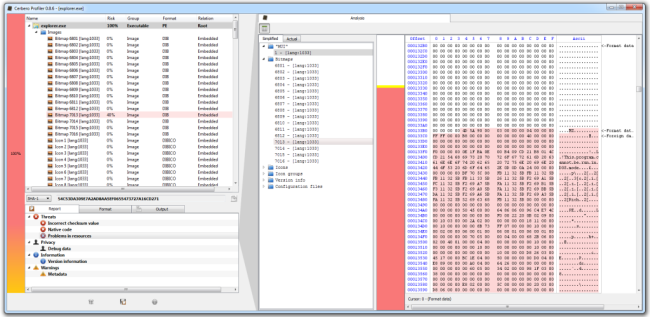
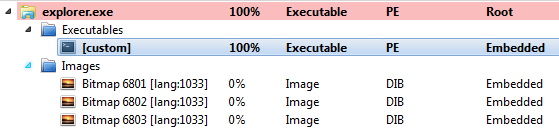
So let’s see a simple test case. What I did is to append a DLL to a bitmap and then replace one of the bitmaps in explorer.exe with my modified one.
I could’ve used any other resource type, or even a PNG or GIF, it wouldn’t have mattered.
The simplified resource tree highlights problems with their risk color, while unsupported types are highlighted in gray.
One can jump to problems with the F2 shortcut, no need to scroll the tree ourselves in search of problems.
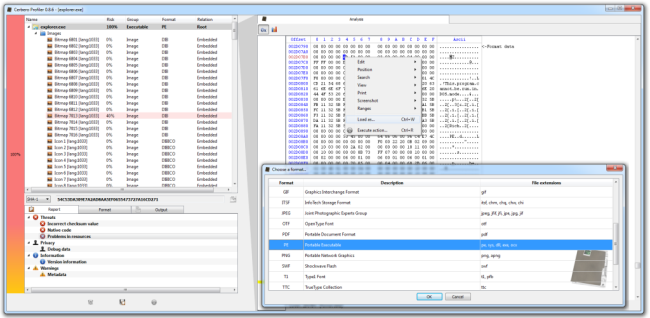
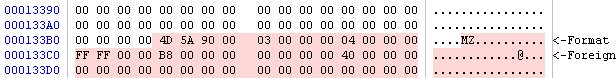
In the screenshot above the analysis shown is for my fake bitmap. As it’s possible to see, the bitmap ends where the red-marked data begins.
In this context it is very easy to just load the embedded PE with the “Load as…” (Ctrl+W) command.
And this gives me the opportunity to mention briefly another nice improvement to the hierarchy view.
As you can see files are now grouped according to their type. This makes it much easier to go over the files or to look for specific types. This behavior is optional and can be changed from the settings.
I think I could’ve presented this new feature with a more interesting real-world case. However, there are still some things to do in order for the new version to come out and there wasn’t enough time. I hope, nevertheless, that you enjoyed the post. 🙂