This font format is very common and mainly found in PDFs. It was used as a vector for native code exeuction in the iOS 4.3 jailbreak. To trigger the vulnerability it was sufficient to open a PDF inside Safari.
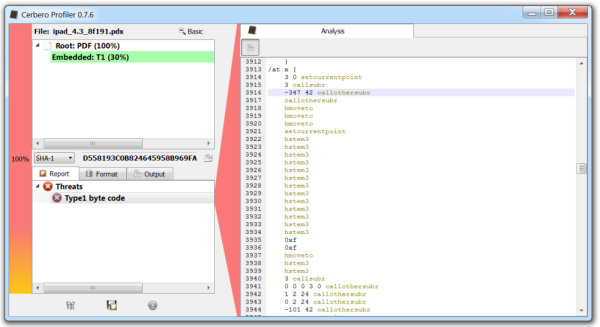
In the screenshot we can see the disassembled code and more precisely the first line of the exploit (a call with a negative number of arguments). As I wrote in this paper and discussed at DeepSec 2011, there are some interesting parts in the Adobe specification of the format. One part explains the reason for Type1 fonts to contain bytecode.
Since Type 1 fonts are expressed as computer programs, they are copyrightable as is any other computer software. For some time, the copyright status of some types of typeface software was unclear, since typeface designs are not copyrightable in the United States. Because Type 1 fonts are computer programs rather than mere data depicting a typeface, they are clearly copyrightable. A copyright on a Type 1 font program confers the same protection against unauthorized copying that other copyrightable works, including computer software, enjoy.
This is important, not only because it tells a great deal about priorities during development (copyright vs security), but also because Type1 is one of the oldest font formats and as such it sets a trend. In fact, the price of the license granted by Adobe to implement such fonts was so high that in 1991 Apple created their own font type (TrueType).
The other part of the specification says something about the security of the parser.
Because Type 1 font programs were originally produced and were carefully checked only within Adobe Systems, Type 1 BuildChar was designed with the expectation that only error-free Type 1 font programs would be presented to it. Consequently, Type 1 BuildChar does not protect itself against data inconsistencies and other problems.