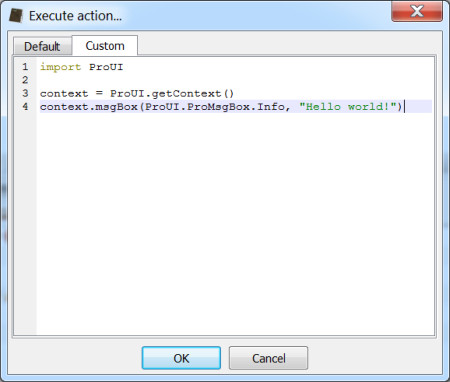
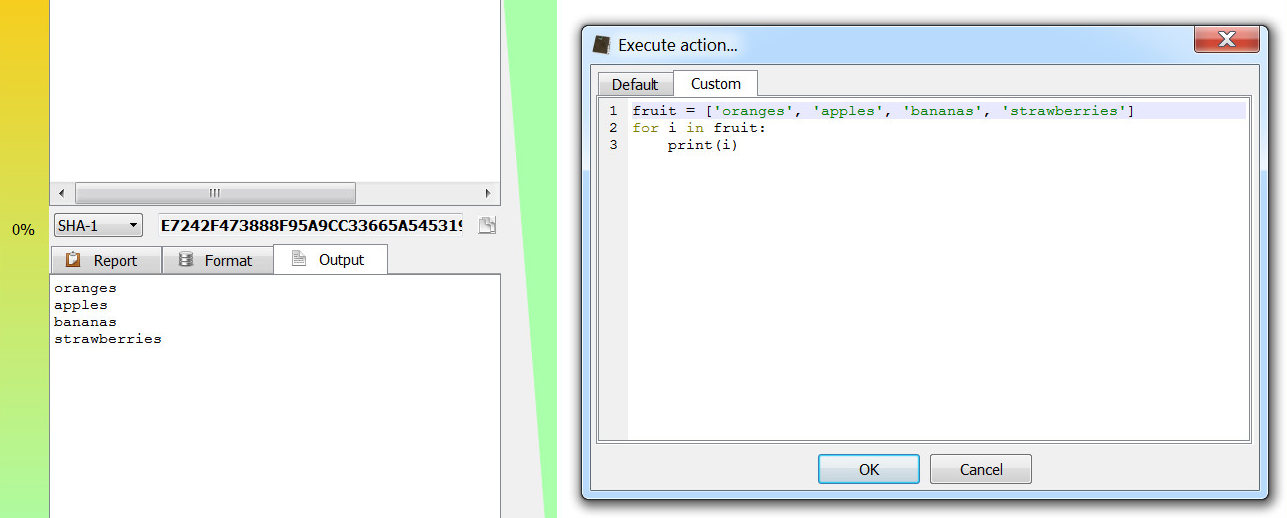
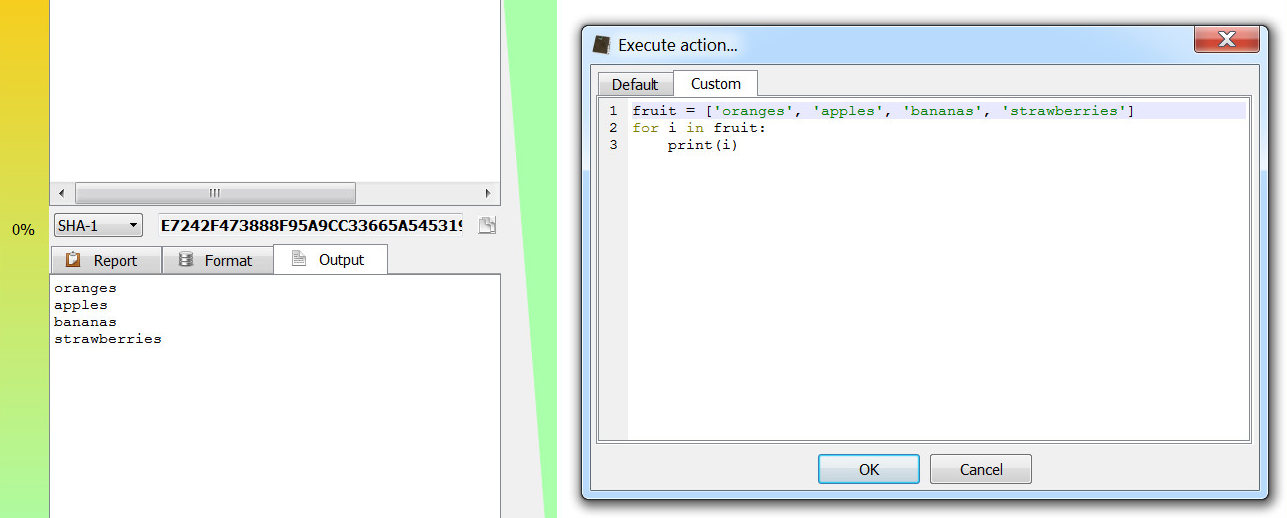
The new version 0.7.3 of Cerbero Suite features a powerful Python 3 SDK, which enables to run custom scripts and actions. Let’s first take a look at a simple script. Just press Ctrl+R (or “Execute action…” in the context menu of a view) and go to “Custom”:
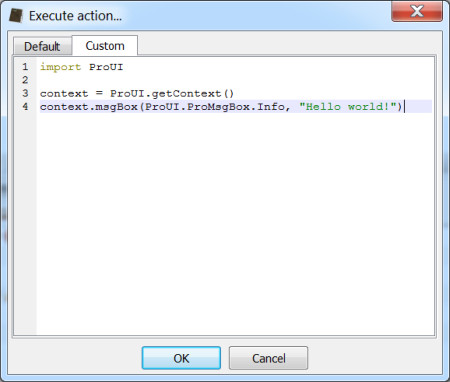
As it is easy to guess, this basic script shows a message box. Message boxes can be used to notify things to the user or to ask him a question. Most of the time they won’t be necessary and the standard output can be used instead. All the output produced by Python will be visible in the output console. In fact, the console will become visible when something is printed to it (this behavior can be changed from the options).
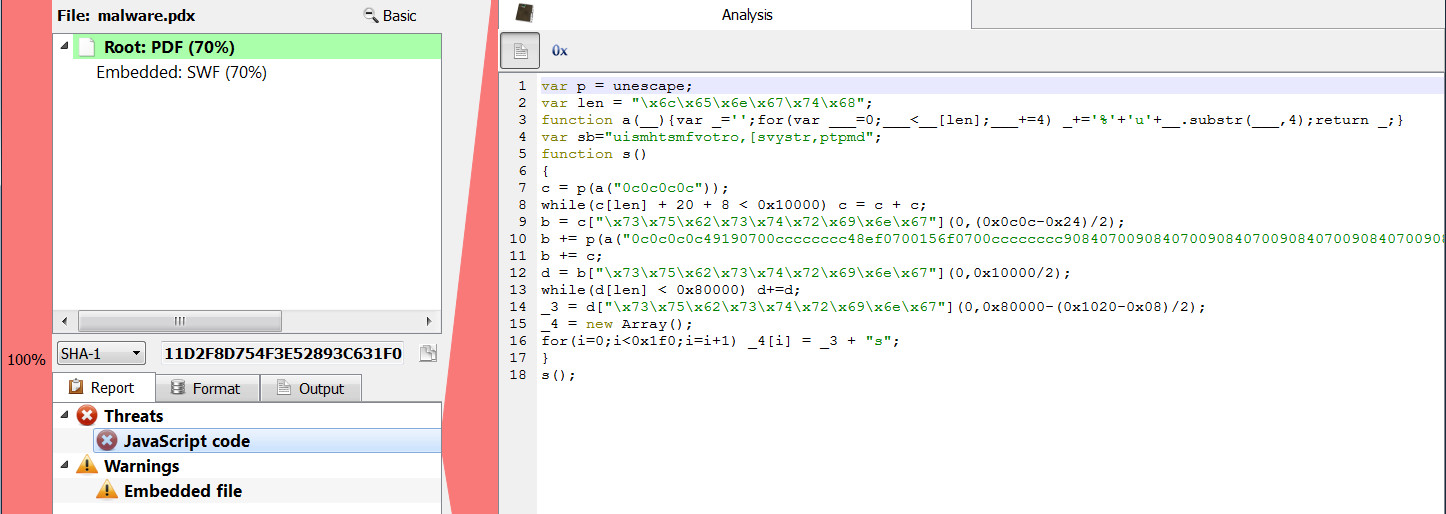
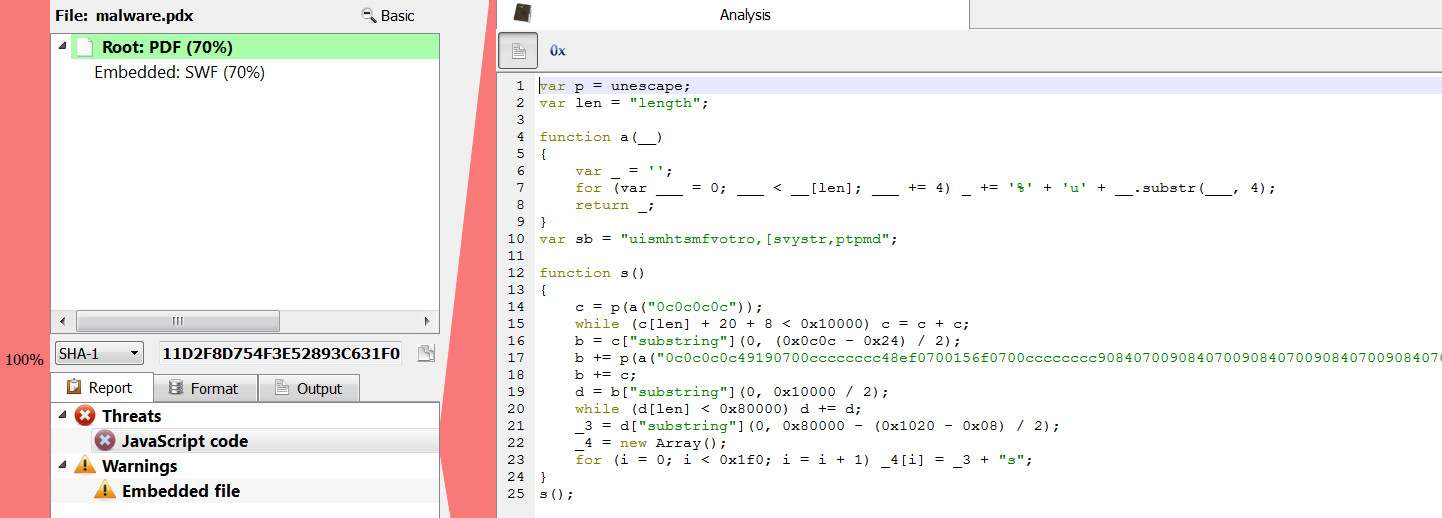
The SDK can be used to retrieve data from views, set their data, create new views and so on. But before looking at a more advanced script, let’s talk about a new feature of Cerbero Suite: actions. For the purpose of demonstration let’s take a malware with obfuscated JavaScript.
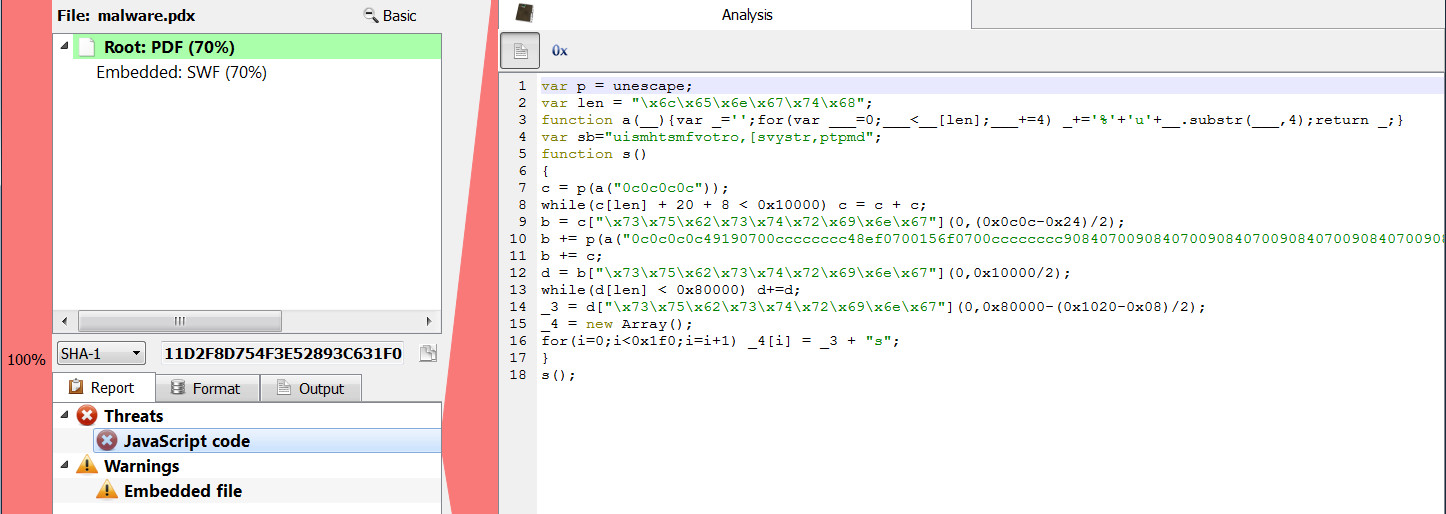
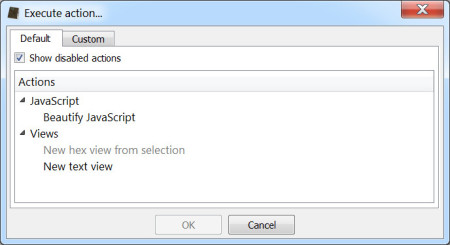
And now let’s again press Ctrl+R in the context of the obfuscated JavaScript.
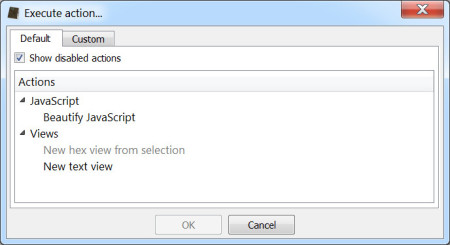
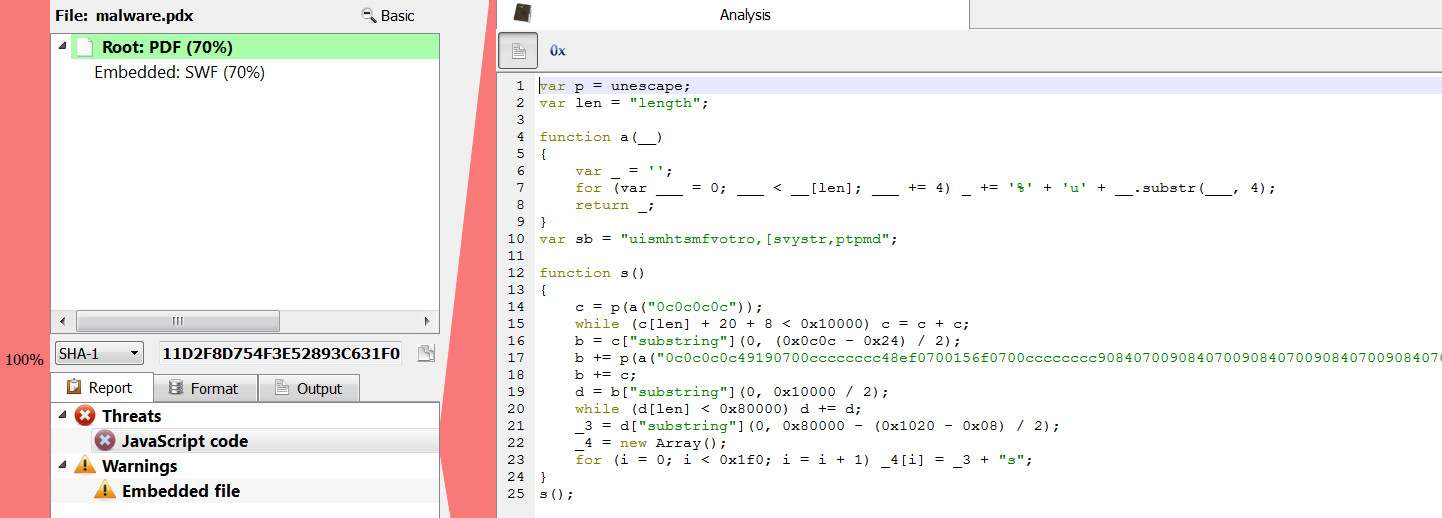
By activating the “Beautify JavaScript” action we will get a beautified version (jsbeautifier.org) of the previously obfuscated JavaScript.
Python actions are defined in the config/actions.cfg file.
[JSBeautify]
category = JavaScript
label = Beautify JavaScript
file = javascript.py
context = text
The section name (JSBeautify) specifies the id of the action and is also the name of the function to be called in file. The file field supports absolute paths as well, otherwise the script will be loaded from plugins/python. The category and label specify in which category inside the execute action dialog the action should be grouped and its description. When the category field is omitted, it will default to “Other”.
The context field is very important as it specifies when the action should be available for use. In this specific case, the action can be used in any text view. An action can also be available in more than one context.
; available both in text and hex views
context = text|hex
; available in text and hex views only when text or data is selected
context = text|hex|sel
; always available even when not in a view
context = any
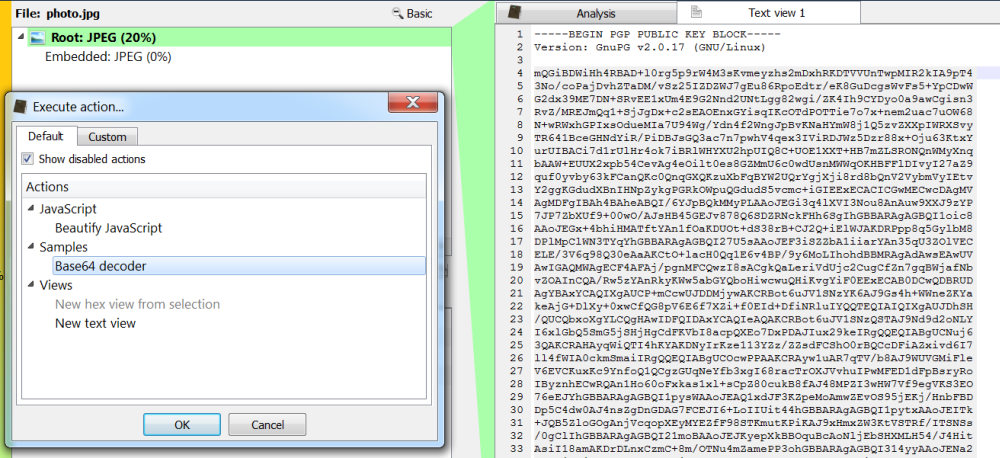
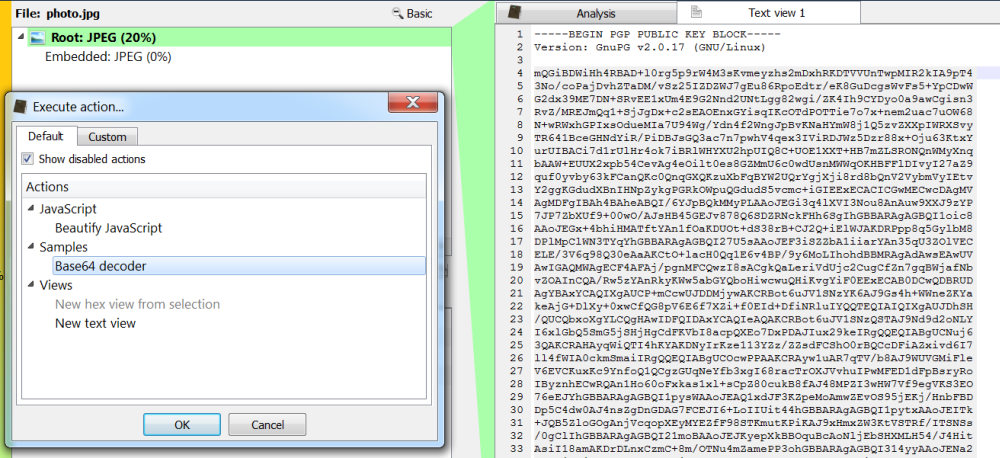
Now let’s see how to create an action which decodes some selected text from base64 and shows the decoded bytes in a new hex view. First it is necessary to define the action.
[Base64Decode]
category = Samples
label = Base64 decoder
file = samples.py
context = text|sel
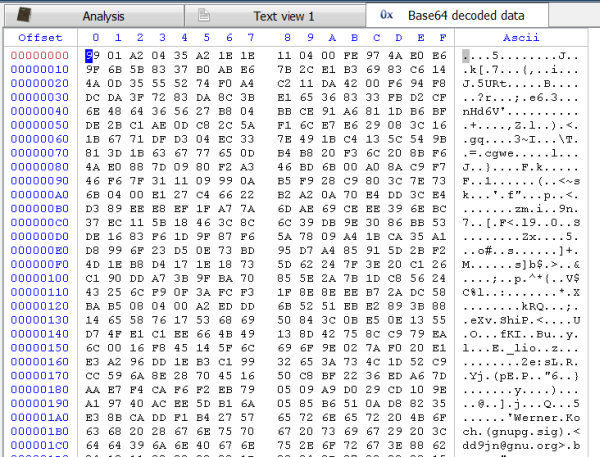
And here’s the Python code.
from Pro.UI import *
def Base64Decode():
context = proContext()
view = context.getCurrentView()
if view.isValid() and view.hasSelection():
text = view.getSelectedText()
decview = context.createView(ProView.Type_Hex, "Base64 decoded data")
import base64
decview.setBytes(base64.b64decode(text.encode("utf-8")))
context.addView(decview)
return 0 Let’s see it in action with a PGP public key.
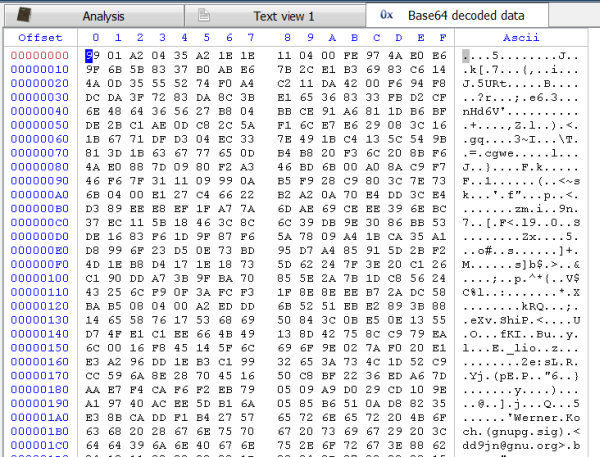
And the decoded data.
Although the SDK is brand new, you will see very soon some new useful actions implemented. 🙂